DARPA Researchers, Students and Industry Partners Demonstrate Micropatching to Secure Legacy Software
In November 2023, students from Colorado State University (CSU) and partners from Assured Information Security (AIS), Cummins Inc., NASA and GRIMM hosted a hackathon at Cummins, Inc., headquarters in Columbus, Indiana, where they challenged students and engineers from several different universities and industries. Participants used a new set of tools to improve the security and functionality of critical infrastructure systems and demonstrate the effectiveness of micropatching to government stakeholders and other industry professionals.
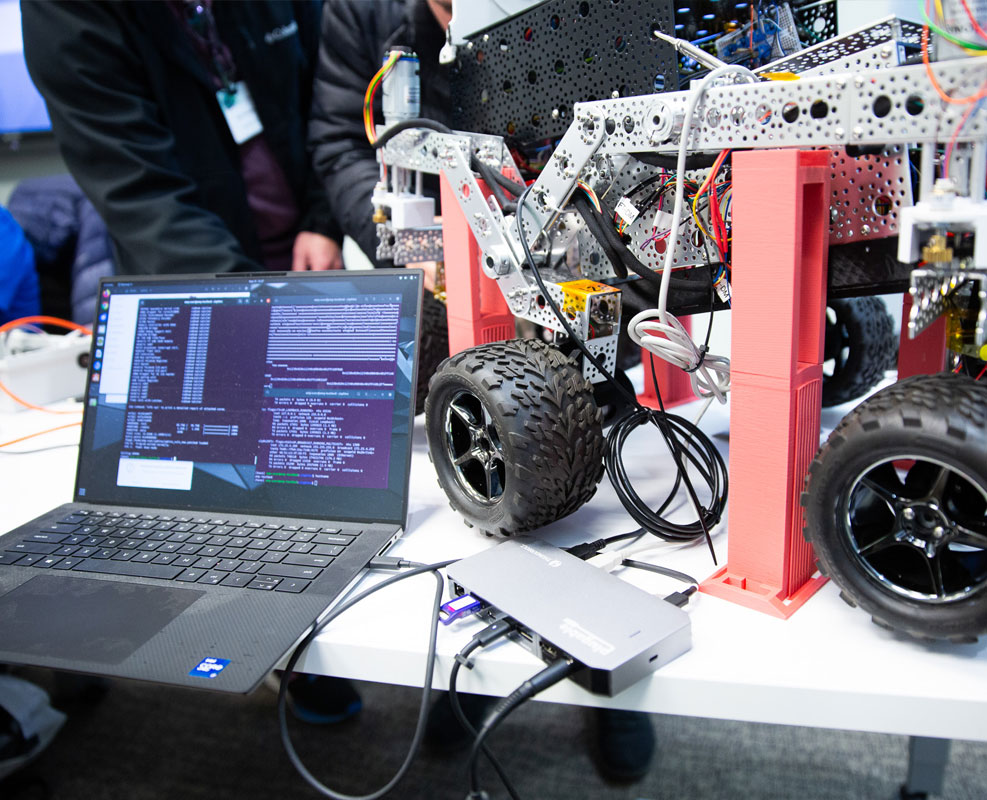
Developed through the Defense Advanced Research Agency (DARPA) Assured Micropatching (AMP) program, participants leveraged these breakthrough tools to patch a series of simulated, real-world vulnerabilities in NASA rovers, satellites, Cummins engine controllers, and supporting computer systems.
In continuation of the groundbreaking efforts propelled by the DARPA AMP program, another hackathon is taking place on March 6-8, 2024, at the ORION NTROPEE facility in Rome, New York, with researchers and engineers from AIS providing mentorship and support.
AMP Tools Revolutionize Bug Resolution and Assurance
Over the past three years, the AMP program has created the capability for rapid patching of legacy binaries in mission-critical systems using novel approaches.
“In navigating the intricate landscape of software development, encountering bugs within binary components poses significant challenges,” said Daniel Salloum, Reverse Engineer III at AIS. “Whether these issues stem from security vulnerabilities or mere logical discrepancies impacting program outcomes, the absence of access to original source code or the complete build-chain complicates resolution efforts.”
Enter the AMP tools, specifically tailored to address such scenarios by aiding developers and analysts in pinpointing root causes, implementing fixes, and ensuring the efficacy of those solutions.
“Traditionally, addressing such challenges would entail deploying reverse or low-level engineers with specialized skill sets,” said Salloum. “However, the AMP tools streamline this process, requiring less specialized knowledge upfront and empowering developers to enact changes directly within the source code. One of the pivotal contributions of AMP lies in providing assurance—a component often overlooked or deemed unattainable due to the absence of original components. In scenarios where the build-chain is lost, conventional software testing becomes unfeasible. Yet, AMP equips end-users with tools to identify binary modifications, assess their expectedness, and navigate rigorous certification processes with confidence. While the primary focus of the program is to support developer-centric operations, the benefits extend to low-level binary-space engineers, expediting their workflows. This collaborative effort has yielded a diverse array of tools catering to various stages of analysis, patching, and testing—a testament to the program’s versatility and efficacy.”
Students Take the Spotlight
The AMP Hackathons are a culmination of multiple years of research being applied by the next generation of engineers to address real security concerns in transportation and aerospace.
At the first event, students and embedded systems engineers were presented with a series of challenge problems representative of vulnerabilities observed in some of our nation’s critical systems. Armed with tools developed under the AMP program, they worked over the course of three days to identify and mitigate these vulnerabilities with limited prior knowledge of the architecture, source code, or techniques required to patch. Researchers from AIS, GRIMM, NASA, and Cummins, Inc., provided mentorship and support as students tackled these challenges.

“Our goal was to patch a bug that caused rovers to miscalculate temperature messages it received, and we needed to ensure we did this in a minimally invasive way and while speeding up the patching process,” said Jake Jepson, Cybersecurity Graduate Research Assistant at CSU. “Reverse engineering in the software space is so broad that no tool is going to work every time. The tools developed through AMP are much more effective which is why our team was able to generate 16 patches in two days. We wanted to push the tools to the limit to not only see if we could develop a patch that worked, but could we develop a patch that works in different ways.”
On the last day, participants shared their experience in using AMP tools to rapidly generate and verify security patches and deploy them to the target systems with minimal impact. Their success demonstrates the potential for broader application of micropatching techniques across legacy software.
“The work, dedication, and innovation of students at the hackathon will have a ripple effect that will undoubtedly be felt in the broader landscape of national security and how we continue to make progress under the AMP program with DARPA,” said Eric Thayer, Chief Engineer at AIS. “Students were able to successfully leverage AMP tools to address real security concerns. This first hackathon marked a significant stride in fortifying critical infrastructure systems against cyber threats. Beyond the event, the broader implications of AMP tools represent a paradigm shift in how we deal with legacy software vulnerabilities, offering rapid and minimally invasive solutions. We’re eagerly anticipating the next hackathon at the ORION NTROPEE facility in Rome, New York.”
(Approved for Public Release, Distribution Unlimited)




